Hybrid attacks on Armenia by two supposedly rival hacking groups
Media expert on hybrid attacks targeting Armenia
Ahead of Armenia’s parliamentary elections scheduled for 7 June, reports of various hybrid attacks have become more frequent. Information security expert Samvel Martirosyan has analysed the activity of two Telegram channels in particular: Armenian Code and Wolves of Turan. He says the same team operates both platforms, despite their apparent rivalry. He adds that their attacks target Armenia.
Martirosyan says he sees a coordinated hybrid attack against Armenia. He does not view as coincidental a statement by Wolves of Turan claiming that it launched “mirror actions” against critical Armenian online platforms “in response to attacks by the Armenian Code team” on Turkish and Azerbaijani websites.
The media expert argues that the motive is to create artificial grounds for a “cyber war” that serves specific geopolitical goals.
We are publishing a translation of Samvel Martirosyan’s article.
- ‘An army of fake accounts backs one of the prime ministerial candidates,’ Armenian fact-checkers say
- Poll: Will Armenia’s ruling party win June election?
- Opinion: ‘Russia has far more leverage over Armenia than over Moldova’
Article by information security expert Samvel Martirosyan
“As the June 2026 Armenian parliamentary elections approach, a sophisticated hybrid operation with the signs of cyberactivities, attacks against critical infrastructure and Foreign Information Manipulation and Interference (FIMI) operation has emerged in the digital shadows.
Two supposedly rival hacking groups — Armenian Code and Wolves of Turan — have appeared on Telegram, engaging in a performative “tit-for-tat” conflict that OSINT analysis suggests is a single, coordinated campaign designed to destabilize the region.”
OSINT (Open Source Intelligence) refers to investigations based on publicly available sources. These include social media platforms such as Facebook, Instagram and LinkedIn, as well as media reports, government registries, forums, maps and satellite imagery. The method involves searching for, collecting and analysing verified data to build profiles or assess a situation. It is a legitimate tool used by journalists, analysts and cybersecurity specialists.
In reality, a single unknown team stands behind the two supposedly opposing hacking groups and carries out the same external operation. Its members most likely speak neither Armenian nor Turkish, but Russian.
Digital twins generated from a single source
While these groups claim to represent opposing nationalist interests, their infrastructure reveals a synchronized birth:
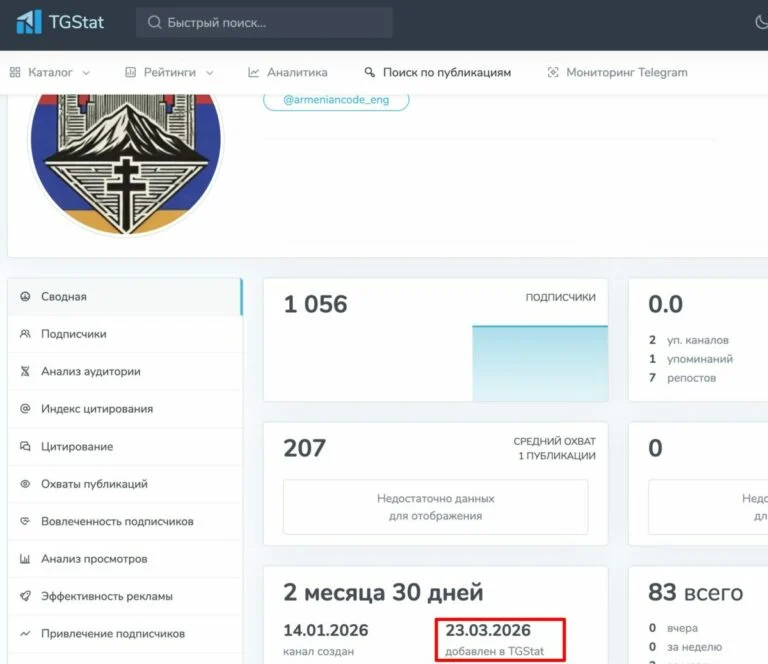
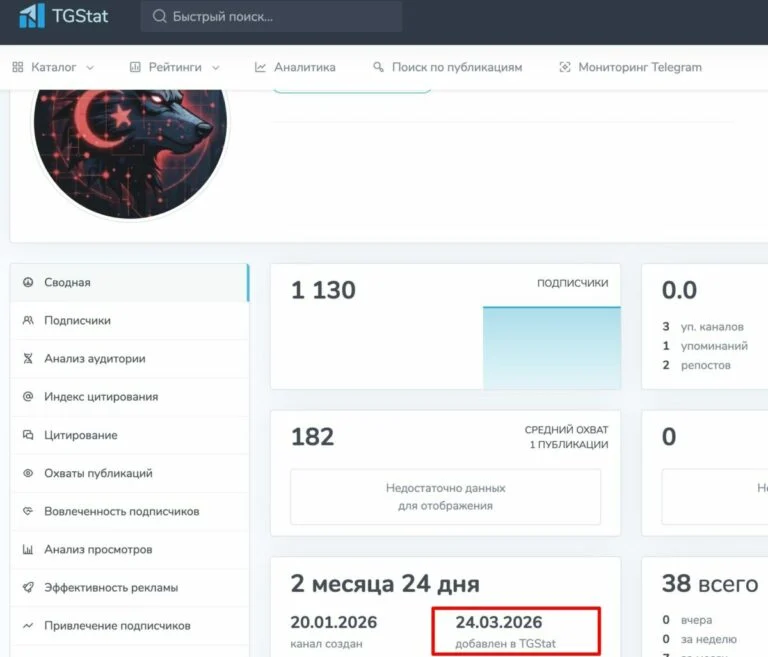
- Infrastructure Mirroring: Both groups registered their channels on the Russian analytical platform TGStat within 24 hours of each other.ой аналитической платформе TGStat с разницей в 24 часа.
- Coordinated Launch: Armenian Code (AC) was created on January 14, 2026. Just five days later, on January 19, the “rival” Wolves of Turan (WoT) emerged. AC channels on Telegram: Eng — @armeniancode_eng , Arm — @armeniancode_am. WoT channels on Telegram:Eng: @Wolves_of_Turan_eng. Tr — @Wolves_of_Turan
Visual and Structural Identity: Both groups operate identical English-translation bot structures and post formatting.
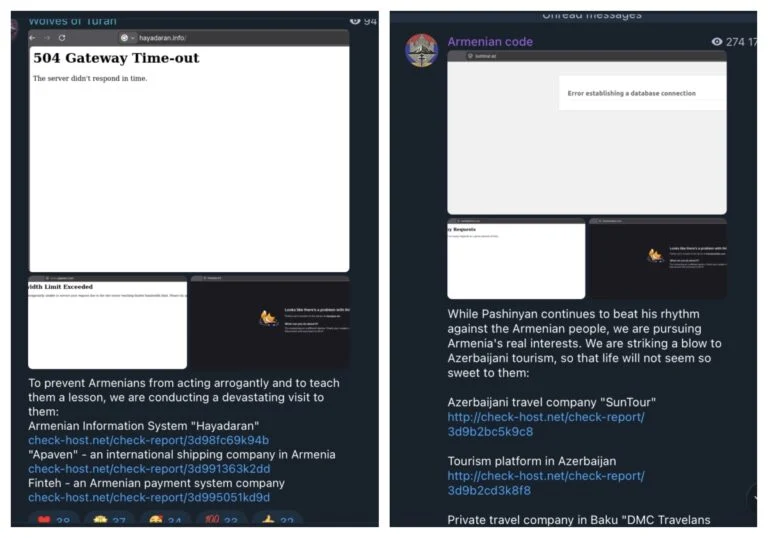
Hackers usually rely on third-party websites to provide objective proof of successful attacks. They create a separate link for each attack, confirming that it targeted a specific website at a specific time.
The Armenian Code and Wolves of Turan channels use the same website for this purpose, which is notable in itself. An even more telling detail suggests both channels share the same administrator. At one point, the common admin accidentally posted identical links on both supposedly opposing channels.
check-host.net/check-report/3d35ec43kb85
check-host.net/check-report/3d35ee5dk6e6
check-host.net/check-report/3d35ed41kc29
In this case, the manipulators became victims of their own tactics and accidentally posted the same links.
Linguistic Fingerprints: The “Russian” Syntax
Despite their posturing as Armenian and Turkish patriots, linguistic analysis by multiple LLMs (Gemini, ChatGPT, Grok) has identified significant markers of Russian-language thought patterns in their English content.
Translation Artifacts: The groups use specific calques (direct word-for-word translations) that are common in Russian political discourse but rare in native Armenian or Turkish digital culture.
Calques from Russian: Literal, slightly awkward English idioms that strongly suggest translation from Russian: “sit idly by with folded arms”, “absorbed it with our mothers’ milk”, “piece by piece”, “we will not miss a single attack and we will take revenge!”, “the call of blood”.
Cyrillic Artifacts: In AC post, the text says: opposition party “Hayk” (Аякве). The inclusion of the Cyrillic spelling Аякве next to the name strongly suggests the original draft was written in a Cyrillic-based script (likely Russian, as “Hayk” is an Armenian name, but the transliteration provided is Russian phonetics. And the real name of the political party is Hayaqve, not Hayk: this also shows automated translation without going deep into details by the unknown operator).
From Noise to Kinetic Impact: The April Escalation
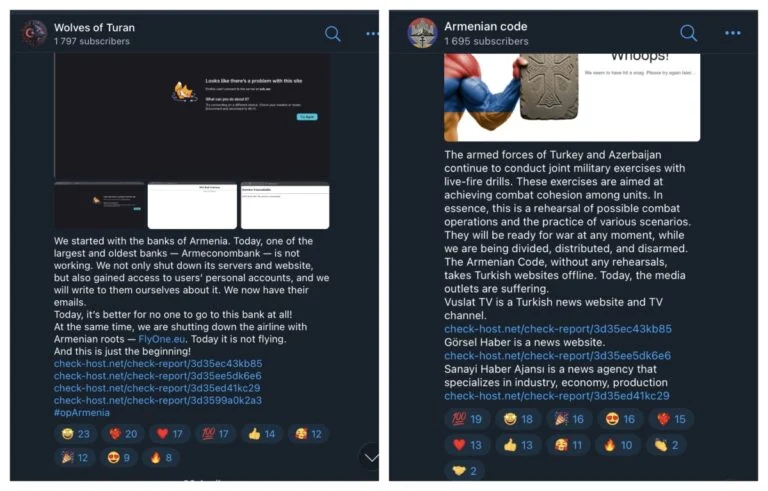
In April 2026, the operation transitioned from information warfare to high-impact DDoS and SCADA attacks.
- Financial Sabotage: Wolves of Turan claimed responsibility for a “collapse of payments” in Armenia, successfully targeting Armenian largest banks, payment systems, insurance companies etc.
- Infrastructure Manipulation: Both groups claim to have accessed SCADA systems to manipulate water reservoirs, heating boilers, and irrigation systems in Baku and Yerevan.
A “Professional” Signature: The ability of a three-month-old “activist” group to paralyze national financial nodes and manipulate industrial control systems suggests state-sponsored or professional mercenary capabilities.
Conclusion: A Manufactured Crisis
The “Armenian Code” and “Wolves of Turan” are not enemies; they are two hands belonging to the same body. By manufacturing a “cyberwar,” the threat actor achieves several geopolitical goals in it`s false-flag operation:
- Economic Disruption: Eroding trust in Armenian banking and fintech stability, state and security institutions.
- Political Polarization: operation designed to inflame the Armenia–Turkey/Azerbaijan cyber (or broader) conflict before the June elections..
In the world of modern hybrid warfare, the most dangerous enemy is the one that pretends to be your own defender while secretly typing from the same room as your “attacker.”
Media expert on hybrid attacks targeting Armenia





















