Who hacked 2,000 websites in Georgia?
The Ministry of Internal Affairs of Georgia says it cannot exclude the possibility that the recent large-scale cyber attack, which resulted in the paralysis of about two thousand websites of various media, governmental and non-governmental organizations on October 28, came from abroad.
“Perhaps the cyber attack was carried out both from Georgia itself and from the territory of another state,” the Interior Ministry said in an official statement.
Hundreds of Georgian websites went offline in the morning of October 28. Among them was the site of the presidential administration of Georgia.
The hacker attack forced Imedi and Maestro TV companies to temporarily suspend broadcasting. The companies say they suffered serious financial and technical losses.
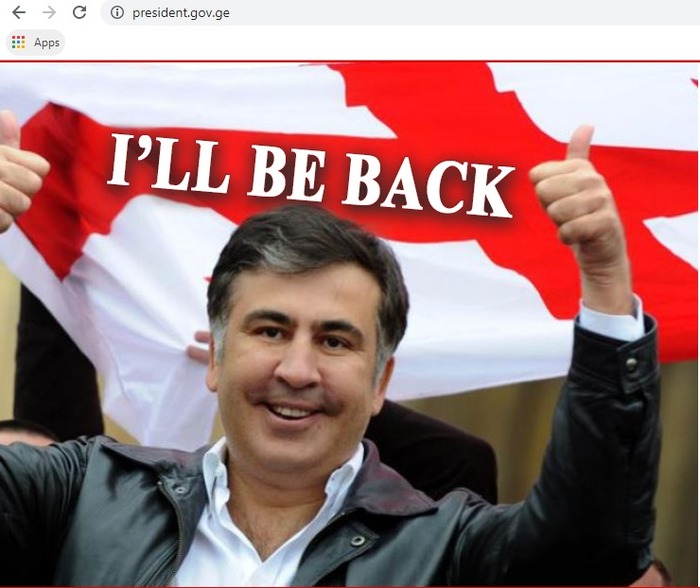
In all cases, photographs of former Georgian President Mikheil Saakashvili with the words “I’ll be back” appeared on the hacked sites.
• When your neighbour is a cyber superpower
• Georgian gov’t using fake news sites, trolls to discredit protests
Here is the website of the Georgian president on the morning of October 28:
To date, most sites have been restored, although some damage is irreparable.
Eliso Kiladze, editor of the Chronika Plus newspaper, said the editorial office lost its archive of the past six years as a result of the hacker attack.
Kiladze believes that the attack was carried out by Russian special services.
“It’s impossible to find a single article written over the past six years on the site,” says Kiladze.
Archive materials on websites have been lost by a number of non-governmental organizations.
The head of the NGO “Society and Banks” Giorgi Kepuladze claims that the archive from their site has completely disappeared.
“I hope the state will be prepared next time for a possible cyber attack. The first similar attack was carried out in 2008. Then the country suffered very serious damage, but apparently no special cyber protection measures were taken,” Kepuladze said in an interview with Rustavi 2 television channel.
Politicians and experts also indicate the state’s unwillingness to repel hacker attacks, and therefore the country faces a global threat:
“We have witnessed an unprecedented cyber attack. Civil security in our state is violated. No citizen can feel protected. More than two thousand sites were disabled, and no one knows what information was stolen and what kind of blackmail can begin in the country”, says Tamar Kordzaia, a member of the Republican Party.
A specialist in cyber technology, Andro Gotsiridaz, in an interview with Radio Liberty, stated that the purpose of such cyber attacks is usually to inflict reputational and psychological damage.
According to him, it is especially disturbing that the sites of government agencies were the targets of the attack:
“In such cases, faith in the state is threatened, since ensuring cyber security is its prerogative. It is possible that this attack was carried out by a hostile state, but this is not a high-tech attack, so to avoid it, to minimize the damage was quite possible.”
According to him, there are several options to avoid this in the future:
“Firstly, sites must be located on secure servers. I do not want to offend anyone, but nevertheless I think it would be better if the sites of government agencies and departments are based on partner countries that use secure servers.
“Secondly, a backup system must exist in order to shut down a damaged site during a cyber attack and immediately launch a backup site.”
The expert focuses on NATO standards. According to him, cybersecurity is one of the most important areas on the path to membership in the alliance:
“The Alliance expressly declares that it will not take seriously a state in which cybersecurity is not ensured … We live under the constant threat of Russian cyber attacks. For example, 70-80 percent of local government employees use e-mail at mail.ru. Government employees use Yandex-taxi. And they are not aware of the possible threats. At first glance, there’s nothing wrong with that, but in fact it’s a big problem in the field of ensuring cybersecurity.”
The Ministry of Internal Affairs on the same day instituted criminal proceedings under Articles 284 and 286, looking into illegal entry into a computer system and / or damage to a computer system and computer data.
“At this stage, as a result of investigative measures, it was established that a cyber attack was carried out, as a result of which the main pages of websites, a so-called Deface, were changed. Most of the victims are provided with hosting services by Georgian private companies,” the Interior Ministry said in a statement.
According to law enforcement officers, they are now questioning everyone who can provide the investigators with important information. The Georgian Interior Ministry is collaborating with colleagues from partner countries.
A Defacement-attack is when the landing page of a website is forcefully changed – this is exactly what happened on October 28 in Georgia.
They are often carried out, for example, by terrorists in the dissemination of jihadist appeals or by so-called activists to publish ideological messages.
2008 – August Hacker War
Georgia is one of the first countries to be the victim of a cyber attack by Russia. This happened in August 2008, together with the acute phase of the Russian-Georgian war.
On August 8, 2008, the sites of the president of Georgia, the government, the Foreign Ministry and the parliament were the target of the attack.
At the same time, information portals were attacked, as well as news sites with a positive attitude towards Georgia (for example, kasparov.ru) and forums.
On August 9, TBC Bank, the largest commercial bank of Georgia at that time, was attacked.
On August 11, not a single government site worked. The presidential website was subjected to defacement-attack – on its first page there appeared fascist symbols and a photograph of Saakashvili stylized as Hitler.
The sites of the National Bank and the Ministry of Foreign Affairs were subjected to attacks of the same type – photos of dictators of the 20th century appeared there.
The Russian publication Meduza several years ago conducted a large-scale investigation of the hacker war that Russia waged in 2008 against Georgia. The publication writes that it was after the attack that the Russian secret services began cooperation with patriotic hackers.
They often use them for various work – sometimes they force them, sometimes voluntarily.
It was the scheme tested in Georgia that the Russian special services used in 2016 when hacking the servers of the US Democratic Party. And in this case, the operation was carried out with the help of freelancers from among hacker patriots.
The publication writes that Russia launched DOS attacks on government sites in Georgia two weeks before the August war, when the situation in the conflict zone in South Ossetia began to escalate.
Meduza writes that in the days of the war, the first hacker attack on Georgian government sites was carried out by Khabarovsk hacker Leonid Stoikov. At first, he acted on his own initiative, having watched a TV programme and wished to help his homeland in the fight against Georgia.
In an interview with Meduza, Stoikov, a.k.a. R0id, admits that it was he who hacked the website of the Georgian parliament and posted a photo of Georgian President Mikheil Saakashvili with Adolf Hitler.
On August 9, patriotic Russian hackers created a special web page called Stopgeorgia.ru.
On this page, they advised other Russian hackers which particular Georgian sites to attack, laid out the necessary links.
As a result, up to 30 hackers gathered on this site. They call themselves representatives of the hack underground and become distributors of ambiguous patriotic slogans.
Stopgeorgia.ru continued its anti-Georgian activities in 2009, when a memorial to a Soviet soldier was blown up in Kutaisi, which interfered with the construction of the building.
Then the hackers again attacked the government sites of Georgia.
“We will not allow the destruction of our historical past,” they wrote in those days and called on other hackers to start a war with the Georgian government.